China is once again tightening regulatory requirements for companies operating in the digital space. The National Measures for the Management of Cybersecurity Incident Reporting took effect on November 1, 2025, and clarify the obligations set forth in the CSL, DSL, and PIPL. This further tightens the compliance regime for companies doing business in China. At… Continue reading Cybersecurity: Tightening of Reporting Requirements
Category: Cyber security
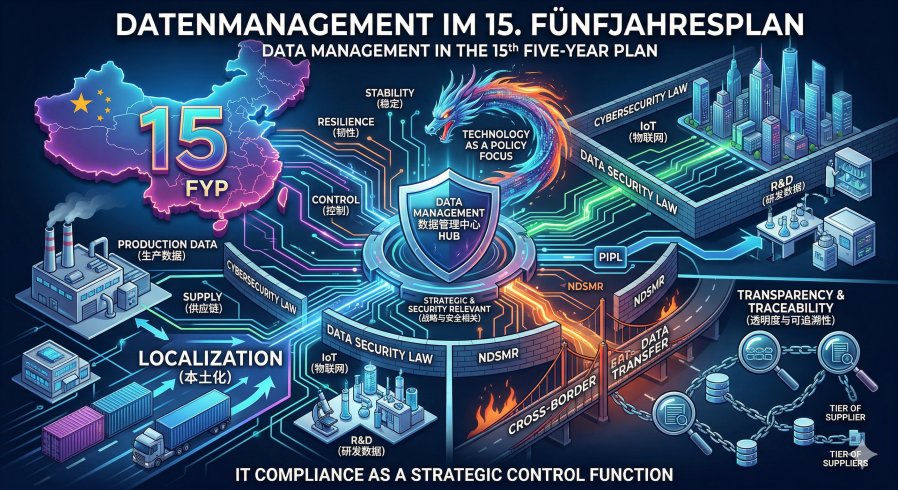
Data in the 15th Five-Year Plan
The 15th Five-Year Plan (2026 – 2030) marks a strategic reorientation in the handling of data. While the economic use of data and the creation of value from it continue to be specifically promoted, data security is simultaneously defined as a fundamental prerequisite for stability. As a result, data is being given greater economic value… Continue reading Data in the 15th Five-Year Plan
Combating cybercrime infrastructure
China is responding to the increasing professionalization and industrialization of digital crime. The country is planning a new law that will target not only individual crimes, but the entire infrastructure behind cybercrime. The background to this is that many digital crimes today are organized through complex structures based on the division of labor. These range… Continue reading Combating cybercrime infrastructure
Stricter requirements for cybersecurity
Since January 1, 2026, stricter requirements have been in force in China under the Cybersecurity Law (CSL). The changes significantly expand the regulatory framework and increase compliance pressure in the areas of cybersecurity, data protection, and AI governance, particularly for foreign companies with ties to China. The key point is the expanded extraterritorial application. While… Continue reading Stricter requirements for cybersecurity
The launch of digital identity
On July 15, 2025, China officially introduced digital identities (digital IDs) – a centralized, state-controlled system for authenticating individuals online. The National Cyber ID Authentication consists of a combination of numbers and letters and is mandatory for using many online services. To register, citizens must upload their identity documents, have their face scanned, and provide… Continue reading The launch of digital identity
Chinese offensive in Europe: Focus on IP and IT
The Allianz Trade Global Survey 2025 clearly shows that Chinese companies are strategically reorienting themselves as a result of the escalating trade conflict with the US and are increasingly turning their attention to Europe. Since American Liberation Day on April 2, 2025, not a single Chinese company with existing supply chains in North America has… Continue reading Chinese offensive in Europe: Focus on IP and IT
New Regulations for Data Audits
On February 14, 2025, the Cyberspace Administration of China (CAC) published the Administrative Measures for Compliance Audits on the Protection of Personal Data, which will come into effect on May 1, 2025. The new regulations apply to all companies in China that process personal data and define clear requirements regarding the frequency of self-assessments as… Continue reading New Regulations for Data Audits
Chinese AI Oversupply
China’s tech industry is currently experiencing an unprecedented investment boom in the field of artificial intelligence, triggered by the use of the advanced model DeepSeek. Xiaomi plans to invest over RMB 7 billion in AI innovation and China Unicom announced RMB 55 billion of investment, with a significant proportion going to AI-driven telecommunications infrastructure modernization.… Continue reading Chinese AI Oversupply
Labeling Requirements for AI-Generated Content
The Cyberspace Administration of China, the Ministry of Industry and Information Technology, the Ministry of Public Security, and the National Radio and Television Administration have jointly issued new regulations introducing mandatory labeling for AI-generated content. These measures will take effect on September 1, 2025, and require platforms to clearly mark content created by AI systems.… Continue reading Labeling Requirements for AI-Generated Content
Proxy cyberwarfare with AI agents
The risk that autonomous AI agents will independently detect vulnerabilities and exploit them as attack vectors is no longer a futuristic scenario – it has become a tangible and rapidly escalating threat. Unlike traditional tools for automated vulnerability scanning, modern AI agents like AutoGPT or SWE-agent operate with a high degree of autonomy. They can… Continue reading Proxy cyberwarfare with AI agents