The new Chinese Five-Year Plan (2026–2030) reveals China’s strategic intention to establish IP not only as a legal instrument, but also as a fundamental pillar of technological sovereignty and economic competitiveness. The plan aims to transform China from a user of IP systems to a leading designer and beneficiary. To this end, IP legal protection… Continue reading IP in the new Five-Year Plan
Tag: Compliance
New Regulations for Data Audits
On February 14, 2025, the Cyberspace Administration of China (CAC) published the Administrative Measures for Compliance Audits on the Protection of Personal Data, which will come into effect on May 1, 2025. The new regulations apply to all companies in China that process personal data and define clear requirements regarding the frequency of self-assessments as… Continue reading New Regulations for Data Audits
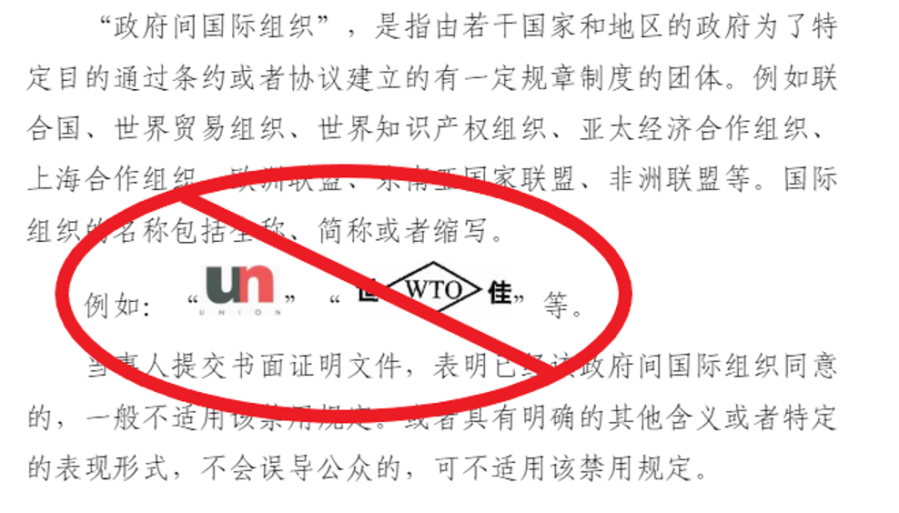
Non-registrable trademarks
In China, there are a number of restrictions on the registration of trademarks. Their purpose is to protect public order, national symbols and international agreements as well as to prevent discriminatory or misleading trademarks. Trademarks that are identical or similar to the names, flags or emblems of countries or national and international organizations are not… Continue reading Non-registrable trademarks
Reporting of cyber security incidents
China regulates the reporting of cyber security incidents in a new law, which is now available in draft form. A key aspect is the reporting obligation for companies that set up or operate networks in China or provide services via networks. Particular attention is paid to the different reporting channels for central bodies, critical infrastructures… Continue reading Reporting of cyber security incidents
Three-year action plan for the Metaverse (2023-2025)
China has now unveiled a comprehensive three-year action plan for the industrial metaverse. The plan prioritizes strengthening the manufacturing industry by integrating innovation with information technology. The momentum of China’s signature innovation drive is maintained, breakthroughs in core metaverse technologies are targeted, and concrete application scenarios are promoted. A particular focus is on security, reliability… Continue reading Three-year action plan for the Metaverse (2023-2025)
Violation of data protection: RMB 50 million fine
On September 6, 2023, after a 14-month review, the Cyberspace Administration of China (CAC) announced that the private platform China National Knowledge Infrastructure (CNKI) was fined RMB 50 million for the unlawful processing of personal data. CNKI is one of the leading academic platforms, digital learning platforms and knowledge bases in China, and its main operators… Continue reading Violation of data protection: RMB 50 million fine
Verification of the processing personal information
On August 3, Cyberspace Administration of China (CAC) issued draft administrative guidelines for privacy-compliant reviews of personal information and related reference points for public expression. The goal of the documents is to provide regulatory oversight of data privacy compliance. However, data processors are also expected to self-regulate and increase their awareness of the need to… Continue reading Verification of the processing personal information
Shanghai improves data protection
Shanghai is raising the level of data protection in the city. A pilot program will classify and tiered data categories and develop catalogs of important data. To this end, the program will identify typical cases, develop general methods, and provide training to meet needs. The background is the Data Security Law (DSL), which includes classified… Continue reading Shanghai improves data protection
Compliance Requirements for Software Development Kits (SDK)
China continues to regulate the collection of private data in apps. For example, the importance of compliance with software development kits (SDKs) has increased significantly. Since June 2021, the authorities have been cracking down on the illegal use of SDKs in apps with SDK Security Special Actions. A software development kit is a collection of… Continue reading Compliance Requirements for Software Development Kits (SDK)
Establishment of Corporate IP Compliance
In the context of building a dual circulation system and creating a unified domestic market, China is guiding all enterprises to strengthen their compliance management to prevent business risks at home and abroad, promote modernization and transformation, and improve competitiveness. The compliance system is to cover areas such as market transactions, environment, human resources, finance,… Continue reading Establishment of Corporate IP Compliance