The requirements of the internationally widely discussed Data Security Law (DSL, effective since Sep 1, 2021) are a challenge for many companies operating in China. To establish a hierarchical protection system for data classification, China’s National Information Security Standardization Technical Committee has issued the National Standard – Guide for Important Data Identification (Draft, hereinafter referred… Continue reading National Standard Provides Insight into Future Data Requirements
Category: Law
Legal Requirements for Vulnerability Management
For some time now, CIOs around the world have been busy fixing the Log4j2 vulnerability. From a technical perspective, there are solutions such as patches and system upgrades. However, vulnerability management is not just a technical issue in China; there are also legal requirements that companies must meet. For example, service providers are required by… Continue reading Legal Requirements for Vulnerability Management
Measures of the Cyber Security Review
China continues to strengthen its control of operators of large Internet platforms. In addition to the regulation on the use of algorithms to influence user behavior, such as recommendation algorithms, which will come into force on March 1, 2022, the Cybersecurity Review Measures will come into force on February 15, 2022. In addition to operators… Continue reading Measures of the Cyber Security Review
Chinese Patent Flood: AI-Powered Search Tool Helps
The ever-growing flood of Chinese-language patents is causing increasing problems for foreign patent attorneys, corporate research and development teams, and in-house counsel. With traditional patent searches, it is not possible to identify and review all relevant IP rights within an acceptable period of time. Limited keywords do not scan the entire technology breadth and may… Continue reading Chinese Patent Flood: AI-Powered Search Tool Helps
Intentional and Punitive Damages in IPR Infringement
Punitive damages are applicable in all areas of IPR infringement and have been steadily improving in PRC legislation in recent years. It is also part of the latest Five-Year Plan through the government’s stated goal of establishing a comprehensive IPR infringement compensation system. The Judicial Interpretation of Punitive Damages for Intellectual Property Rights to Punish… Continue reading Intentional and Punitive Damages in IPR Infringement
IP Protection in the Chinese Metaverse
The topic of IP in the metaverse (metaverse) is gaining importance in China. The drivers are the Chinese technology groups, above all Baidu, Tencent, Alibaba, ByteDance and NetEase, which are currently racing against each other with massive metaverse trademark applications. Tencent alone has filed around 100 applications. Baidu, for example, has applied for the term Metaapp as a trademark, Alibaba for the trademark Ali Metaverse, and NetEase for the NetEase Metaverse. NetEase Group’s trademark applications… Continue reading IP Protection in the Chinese Metaverse
Important Data: More Duties for Processing
China is fleshing out its data protection rules. The Network Data Security Management Regulation (Draft for Comments), published in November 2021, provides more detailed guidance regarding the obligations of processors of important data. Data is divided into general data, important data, and national core data. Important data refers to data that may jeopardize national security… Continue reading Important Data: More Duties for Processing
IP Protection in New Areas
Intellectual property protection has always been high on the Chinese agenda. For example, the Made in China 2025 strategy aims to transform Chinese enterprises from manufacturers into owners and creators of intellectual property in the global economy. In September and October 2021, China published the Outline of Building an IPR Powerhouse (2021-2035) and the 14th… Continue reading IP Protection in New Areas
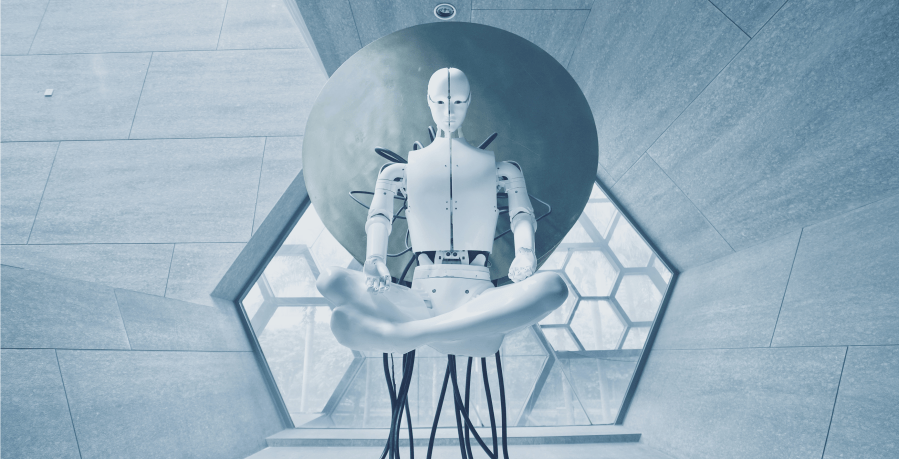
China’s Triumph in Robotics
The Middle Kingdom continues to gain ground in the research and development of the robotics industry and can hardly be caught up. This development is clearly visible when looking at the total number of patents in this field. China leads the world in this area by a significant margin, having filed nearly three times as… Continue reading China’s Triumph in Robotics
Data Export Security Assessment: All Data Processors Are Involved
With the enactment of China’s Cybersecurity Law (CSL), Data Security Law (DSL), and Personal Information Protection Law (PIPL), security management and assessment of cross-border data transfer became a key issue. Following these three laws, China’s Cyberspace Administration (CAC) published the Measures on Data Export Security Assessment (Draft for Comments) on October 29, 2021, which provides… Continue reading Data Export Security Assessment: All Data Processors Are Involved